As businesses go digital, networked computing has been evolving rapidly. Earlier, system administrators had to manually install software, change configuration, and manage every server manually. It did not just require manual effort, but also complicated coordination. The increasing number of data centers made the task a lot more time consuming and complex. This led to the rise of tools that can manage all of this without the need to manually do it.
Here’s where Ansible steps in to drive away complexity and increase productivity by efficiently managing hordes of serves. Automation has become a critical factor for digital transformation. It improves speed, scale and stability.
What is Ansible?
Ansible is an IT automation tool. It is easy to set-up and known for its flexibility. It manages all those repetitive tasks efficiently, freeing up the admin time to do more meaningful tasks. Developed by Michael DeHaan, it is also a part of Fedora distribution of Linux that is owned by Red Hat. Though a company called Ansible, Inc. was set-up to support the open source platform, it was later acquired by Red Hat in October 2015.
What it does?
Ansible is a simple tool catering to many IT automation needs including configuration management, app deployment and intra-service orchestration.
Provisioning: Automates tasks like setting up numerous servers in your infrastructure. It doesn’t matter whether the systems are hosted on servers or cloud.
Configuration Management: A simple solution for configuration management that is designed to be minimal in nature, consistent, secure, and extremely reliable. The configurations are simple data descriptions, and you don’t need to learn a coding language specifically. It only requires a password or SSH key to start managing systems without the need for agent software. This also helps avoid the problem of “managing the management”, which is quite common in automation systems.
Application Deployment: Deploying multi-tier applications from one common framework. All you need to do is write simple task description, and not custom codes.
Orchestration: Ansible brings the required order to how multiple configurations interact and how they can be managed as one entity.
Security policy: Security is critical. Ansible lets you define the systems for security. The Playbook syntax will allow defining security to any part of the system, be it custom policies or firewall rules. It lets you update a security patch from a vendor across the entire infrastructure using a simple command.
Why Ansible?
Simplicity: There are other automation tools out there, but there are many factors that set Ansible apart. It is easily readable by human and doesn’t require any special coding skills. It can be managed from one controller machine, without the need to install client software on the node machines.
Powerful: Though simplicity lies at its core, it is powerful enough for app deployment, configuration management and workflow orchestration.
Agentless: Ansible has an agentless architecture. It uses OpenSSH and WinRM. It doesn’t require any agents.
How it works?
Ansible models your infrastructure in such a way that all your systems inter-relate instead of simply managing one system at a time. It is easy to deploy and uses simple YAML language in the form of Ansible Playbooks. This means you can deploy your jobs in simple language.
It then connects the nodes resulting into small programs called Ansible modules. These modules are then executed using SSH and then pushed out. The library of the modules can be on any machine, without the need for databases or servers. Ansible has ‘authorised_key’ module with the ability to control access given to machines.
The inventory is managed in simple files and you can use simple INI files that places all your machines in groups and you can easily add more. The simple yet powerful automation language used by Ansible is called Playbooks. It can be called an instructions manual that tells Ansible what to do, even if a new machine is connected each time. Written in YAML, it is human readable, and one can easily start writing powerful playbooks. It lets you set specific roles for certain server groups.
It is available for free and runs on Linux, Mac, or BSD, but it also has an enterprise product called Ansible Tower. Ansible Tower is a web-based solution aimed at making Ansible easier to use for IT teams of all kinds. It serves as a hub for automation tasks.
Tower basically lets you control access to who can access what. It lets you share SSH credentials without someone being able to transfer those credentials and logs all of your jobs. It comes with a dashboard displaying everything going on in your Ansible environment.
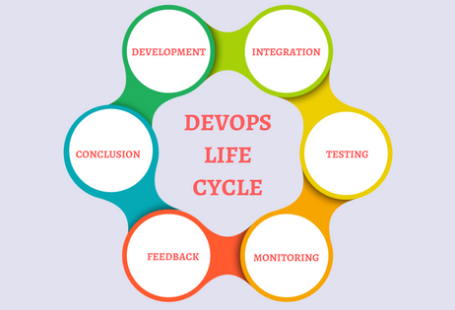
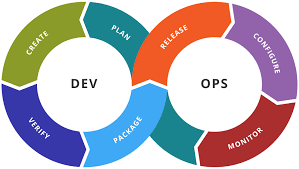
Ansible in Devops
Devops is a software engineering process that aims at brining development and software operation under one roof. Basically, Devops advocates automation and monitoring at every stage. It aims at shorter development cycles and increasing deployment frequency. Discussions around devops would usually include automation tools like Puppet and Chef, but Ansible has now made it to the list.
Ansible is simple to setup and ideal for smaller companies, and removes the need for a dedicated system admin as anyone can operate it. In larger companies, it is used in combination with either Chef or Puppet. Factors like agentless architecture, easy to learn, ease of use have made it a recommended name at Devops.
NASA Case study
A case study published reveals how Ansible allowed NASA to gain significant cost savings.
Challenge: A case study involving Ansible and NASA, the National Aeronautics and Space Administration, the agency of the United States government responsible for space program, aeronautics and aerospace research, reveals that the latter had to move some applications from traditional data centers (hardware) to cloud. This would save costs and also offers better agility. It led to creating an environment with multiple virtual private clouds that weren’t easy to manage. Even a small task looked strenuous.
How Ansible came to the rescue: Ansible Tower was deployed to manage and schedule the cloud environment, and the result led to better operations and security. It increased efficiency, for example, nasa.gov that earlier took one hour to update reduced to just five minutes. Patching updates was a 45 minutes tasks, unlike multiday process seen earlier. It allowed real-time disk and RAM monitoring and provisioning OS accounts went to under 10 minutes. Application stack setup went to under 10 minutes per stack from 1-2 hours that were needed earlier.